Network Security Practices - Fortify Your Digital Fortress
Our dependence on secure networks has skyrocketed in our hyper-connected world. Sensitive data traverses corporate landscapes, personal information finds its home in cloud storage, and the very foundation of our digital lives rests upon the stability and security of interconnected systems. Yet, with this ever-expanding digital footprint comes a heightened vulnerability to cyber threats. Malicious actors lurk online, constantly probing for weaknesses to exploit.
Fortunately, a robust defense can be established through the implementation of network security best practices. By adopting a multi-layered approach that combines preventative measures, vigilant monitoring, and a commitment to user education, organizations and individuals alike can significantly reduce their exposure to cyberattacks.
The first line of defense in any network security strategy is network segmentation. This involves dividing the network into smaller, logically isolated zones. Each zone can group devices with similar security needs, such as a zone for public-facing web servers or another for internal workstations. By compartmentalizing the network, a breach in one zone is contained, preventing lateral movement and minimizing potential damage.
Access control further bolsters network security. This principle dictates that only authorized users and devices should be granted access to specific network resources. Implementing strong user authentication mechanisms, such as multi-factor authentication (MFA), ensures that only legitimate users can access sensitive data. Additionally, role-based access control (RBAC) restricts user permissions based on their job function, granting them access only to the resources they absolutely need to perform their tasks.
Firewalls act as the gatekeepers of your network, meticulously examining all incoming and outgoing traffic. They are configured with security rules that define which traffic is allowed and which is blocked based on pre-determined criteria. Firewalls shield your network from unauthorized access attempts, malware infiltration, and other malicious activities.
Intrusion Detection/Prevention Systems (IDS/IPS) work in tandem with firewalls to provide an extra layer of security. IDS systems continuously monitor network traffic for suspicious activity, alerting network administrators to potential threats. IPS systems take a more proactive approach, actively blocking malicious traffic before it can gain access to the network.
Encryption scrambles data using a complex algorithm, rendering it unreadable to anyone who doesn’t possess the decryption key. This is paramount for protecting sensitive information, both while it’s being transmitted across the network (data in transit) and when it’s stored on network devices (data at rest).
HTTPS (Hypertext Transfer Protocol Secure) is a widely used encryption protocol that safeguards communication between web servers and web browsers. It ensures that any data transmitted, such as login credentials or credit card information, remains confidential. Organizations should also leverage encryption technologies like Secure Sockets Layer (SSL)/Transport Layer Security (TLS) to encrypt sensitive data at rest on servers and storage devices.
Software vulnerabilities are a constant target for attackers. Fortunately, software vendors regularly release security patches to address these vulnerabilities. However, the effectiveness of these patches hinges on their timely installation. Patch management is the systematic process of identifying, acquiring, and deploying security patches across all network devices and software applications. Organizations should establish a regular patching schedule, prioritizing critical vulnerabilities and ensuring all systems are updated promptly.
Even the most robust technical safeguards can be undermined by human error. Social engineering attacks, for instance, prey on human vulnerabilities to trick users into revealing sensitive information or clicking on malicious links. Security awareness training empowers users to identify and mitigate these threats. By educating employees on best practices such as password hygiene, phishing email red flags, and the importance of reporting suspicious activity, organizations can significantly reduce their susceptibility to social engineering scams.
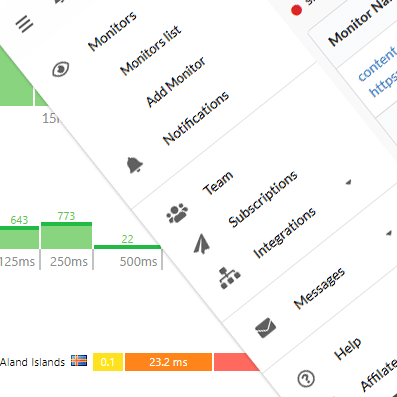
Network security is not a static endeavor; it’s an ongoing process that demands constant vigilance. Security Information and Event Management (SIEM) tools aggregate logs and events from various network devices, providing centralized monitoring and alerting capabilities. Security teams can leverage SIEM tools to identify suspicious activity, investigate potential incidents, and take swift action to contain threats.
A well-defined incident response plan outlines the procedures to be followed in the event of a security breach. This plan should encompass steps for identifying the breach, containing the damage, eradicating the threat, and implementing corrective measures to prevent future occurrences. Regularly testing and updating the incident response plan ensures a coordinated and efficient response to security incidents.
Network security is not merely a technical challenge; it’s a cultural imperative. By fostering a culture of security awareness within an organization, employees become active participants in safeguarding the network. This collaborative approach, where security is seen as everyone’s responsibility, strengthens the overall defense posture.
Remember, security is an ongoing journey, not a destination. By embracing best practices, remaining vigilant, and adapting to evolving threats, organizations and individuals can create a robust digital fortress, safeguarding their valuable data and ensuring a secure and thriving online presence.